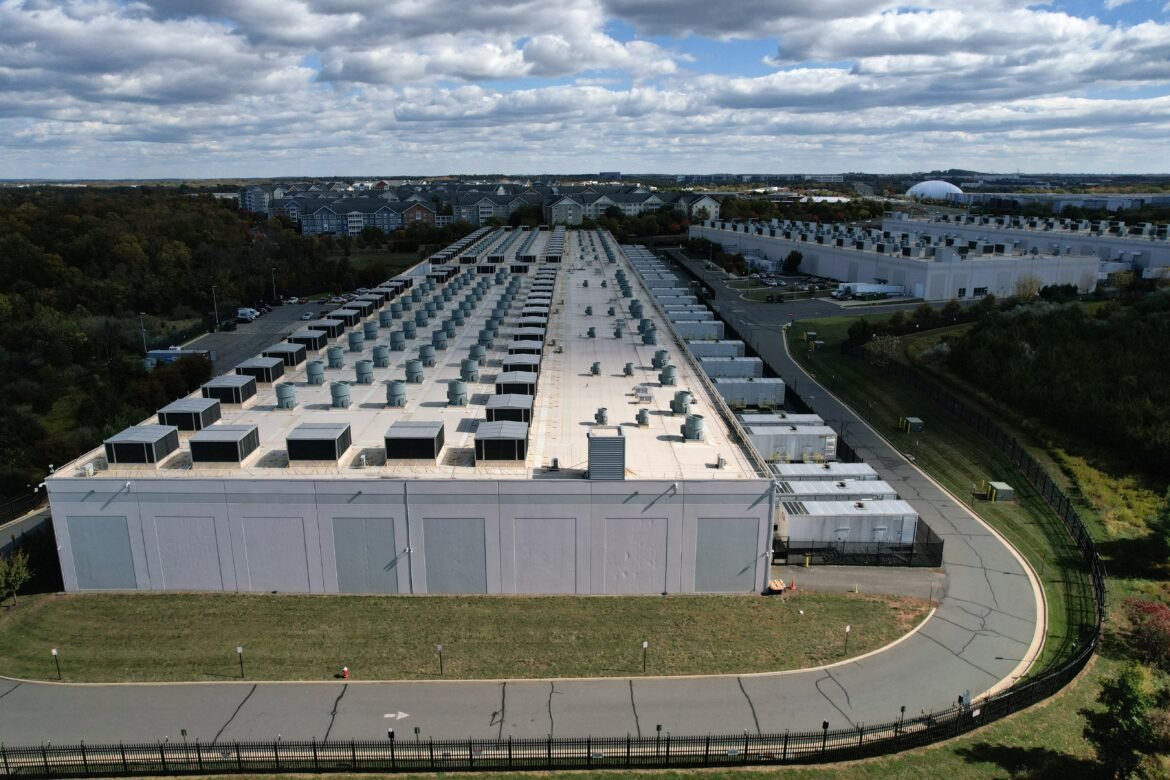
Conflict between the United States and Israel against Iran turns one month old While fleeing a missile attack from Iran, some Israelis with Android cell phones received a message with a link to a supposed real-time information application about bomb shelters. But instead of offering a useful application, the link downloaded a malicious file that gave hackers access to the cell phone’s camera, location and all user data. 🗒️ Do you have any reporting suggestions? Send to g1 The operation attributed to the Iranians demonstrated sophisticated coordination on the cyber front of the conflict that pits the United States and Israel against Iran and its digital representatives. As they seek to use cyber capabilities to offset their military disadvantages, Iran and its supporters demonstrate how disinformation, artificial intelligence and digital intrusions are now embedded in modern warfare. The fake messages received recently appeared to have been timed to coincide with the missile strikes, representing an unprecedented combination of digital and physical attacks, said Gil Messing, chief of staff at Israeli cybersecurity firm Check Point Research. “This was sent to people as they ran to shelters for cover,” Messing said. “The fact that it’s synchronized and at the same minute is something new.” Experts have said the digital feud is likely to continue even with a ceasefire because it is easier and cheaper than conventional conflict and is not designed to kill or conquer but to spy, steal and intimidate. High-Volume, Low-Impact Cyberattacks Although large in number, most war-related cyberattacks have caused relatively limited damage to economic or military networks. But they have put many companies on the defensive, forcing them to quickly patch old vulnerabilities. Nearly 5,800 cyberattacks from about 50 Iran-linked groups have been tracked so far, according to investigators at Utah-based security firm DigiCert. Most have targeted US and Israeli companies, but some have targeted networks in Bahrain, Kuwait, Qatar and other countries in the region. Many cyberattacks are blocked by newer cybersecurity measures, but they can cause serious damage to organizations with outdated systems and place demands on resources even when they are unsuccessful. They also have a psychological impact on companies that may do business with the military sector. “There are many more attacks going on that are not being reported,” said Michael Smith, director of field technology at DigiCert. See the demands of the US and Iran to end the war A group of pro-Iran hackers said on Friday (27) they had hacked into the account of FBI director Kash Patel and published what appeared to be old photographs, a resume and other personal documents of the head of the agency. Many of these records appeared to be more than a decade old. It’s similar to many of the cyberattacks linked to pro-Iran hackers: flashy and designed to boost morale among supporters while undermining the opponent’s confidence, but without much impact on the war effort. These high-volume, low-impact attacks are “a way of telling people in other countries that you can still reach them even if they are on another continent. This makes them more of an intimidation tactic,” said Digicert’s Smith. Critical structures as targets Iran is likely to attack the weakest links in American cybersecurity: supply chains that support the economy and the war effort, as well as critical infrastructure such as ports, rail stations, water systems and hospitals. Iran is also targeting data centers with cyber and conventional weapons, showing how important these locations are to the economy, communications and military information security. Aerial view of an AWS data center in the US-EAST-1 region in northern Virginia, USA Reuters/Jonathan Ernst This month, hackers from the Iran-supporting group Handala claimed to have hacked the American medical technology company Stryker and claimed the attack was in retaliation for alleged US bombings that killed Iranian schoolchildren. In another attack, hackers blocked a healthcare company’s access to its own network using a tool that US officials have linked to Iran, researchers at US cybersecurity firm Halcyon recently said. In this case, the hackers never demanded a ransom, suggesting they were motivated by destruction and chaos rather than profit, the researchers revealed. Coupled with the Stryker attack, “this suggests a deliberate focus on the medical sector rather than targets of opportunity,” said Cynthia Kaiser, senior vice president at Halcyon. “As this conflict continues, we should expect this targeting to intensify.” Artificial intelligence is providing a boost Artificial intelligence can be used to increase the speed of cyberattacks and allow hackers to automate much of the process. But it is in disinformation that AI has truly demonstrated its corrosive impact on public trust. Supporters of both sides have disseminated false images of atrocities or of decisive victories that never happened. A deepfake of sunken US warships has racked up more than 100 million views. It is #FAKE that images show elite American military personnel captured by Iran What is deepfake and how it is used to distort reality What is #FACT and what is #FAKE in the war between the United States and Iran in the Middle East Authorities in Iran have limited internet access and are working to shape Iranians’ view of the war with propaganda and disinformation. Iranian state media, for example, began labeling real images of the war as fake, sometimes replacing them with their own manipulated images, according to research by NewsGuard, an American company that monitors disinformation. Increasing concerns about risks posed by AI and intrusions led the US State Department to create the Office of Emerging Threats in 2025, focused on new technologies and how they could be used against the US. It joins similar efforts already underway at agencies such as the Cybersecurity and Infrastructure Security Agency (CISA) and the National Security Agency (NSA). AI also plays a role in defending against cyberattacks by automating and speeding up work, Director of National Intelligence Tulsi Gabbard recently told Congress. Technology, she said, “will increasingly shape cyber operations, with operators and defenders using these tools to improve their speed and effectiveness.” Despite Russia and China being seen as greater cyber threats, Iran has still launched several operations against Americans. In recent years, groups working for Tehran have infiltrated President Donald Trump’s campaign email system, attacked water systems in the United States and attempted to break into networks used by the military and defense contractors. They have also posed as American protesters online as a way to covertly encourage protests against Israel. Authorities in Iran have limited internet access, and the US has raised concerns about risks posed by AIAuthorities in Iran have limited internet access, and the US has raised concerns about risks posed by AI Reuters/Dado Ruvic
Source link
Fake application, deepfakes and attacks on data centers: what the ‘digital war’ between Iran, USA and Israel looks like
21